ITIL training describes service asset and configuration management as one of the key processes in the ITIL Service Transition stage of the ITIL lifecycle. It requires certain tools for efficiency and effectiveness. ITIL online courses stipulate many tools that can assist the service asset and configuration management process. One of these tools is the Definitive Media Library or DML. A DML is one or more locations in which the definitive and approved versions of all software configuration items are securely stored.

Details and information of configuration items are included in configuration records in a configuration management system. However, this information and details of the configuration items can be located in storages, external disks, CD-ROMs, DVD-ROMs etc. For instance, a Microsoft Office CD-ROM is a configuration item of a company and stored in a CD-ROM. The definitive media library is the location of where all these configuration item data and details are stored.
It contains associated configuration items
The DML may also contain associated configuration items such as licenses and documentation. For instance, if a Microsoft Office license can be installed on a computer of a company only if Microsoft Windows is installed first. This is a relationship between two licenses and this kind of association can be included in the definitive media library.
It is a single logical storage area
The definitive media library is a single logical storage area even if there are multiple locations. All software in the definitive media library is under the control of change and release management and recorded in the configuration management system. There can be several storages and physical locations to store information about configuration items of an IT service provider. The definitive media library covers all storages and physical locations that include details and associations of configuration items. Since the definitive media library must have the latest information about each configuration item, whenever a release, revision or information of a configuration item changes, it must be updated in the DML as well.

Only software from the definitive media library can be used
Only software from the definitive media library is acceptable for use in a release. Let’s consider a service. Depending on new requests, fixed problems etc, newer releases and revisions of the service will be produced and published. Since the association of this service with other configuration items are stored in the definitive media library, only the available version in the definitive media library can be used in a release.
Relationships in a definitive media library
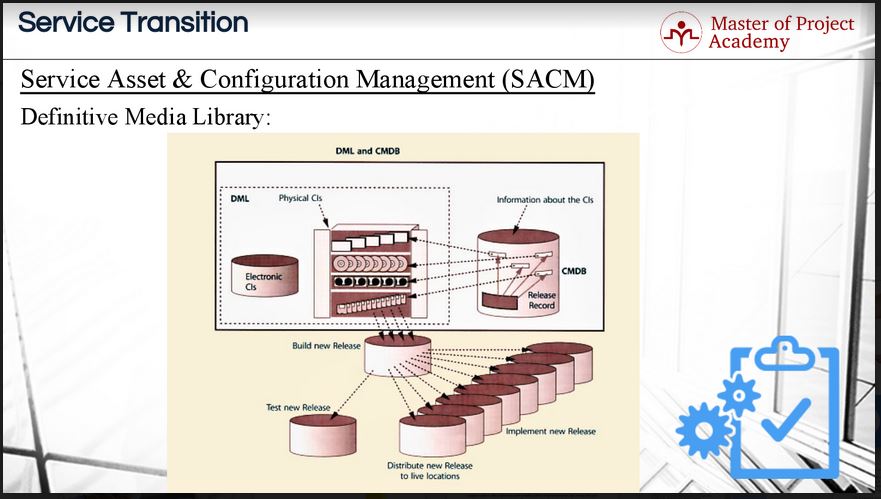
This figure shows the relationship of definitive media library, configuration management database and release management. As you see, electronic and physical configuration items are stored in the DML and information about each configuration item and their relationship with each other is stored in the configuration management database. When there will be a new release deployment, only available releases existing in the definitive media library can be used to build a new release. After a new release is built, testing begins to check whether there are any problems before implementing this release. If there is not a problem during testing, implementation of tested release starts respectively. The new release is updated in the DML.
How to start a definitive media library
First, the IT service provider needs to decide what the organization consider “definitive media.” Is it software, licenses, documentation or something else? The organization needs to decide what to put under DML control. Remember that the DML effectively works as a specialized Configuration Management Database. Therefore, all the rules of configuration management, ITIL change management, and release/deployment management would also apply here. When you have your definition, you need to identify all the configuration items that are now classified as definitive media. Once identified, they are controlled by adding information and attributes about the media into a DML tool. There are many DML tools available on the market. Physical copies of boxed or purchased software can be gathered together for storage in a locked cabinet etc. Now the regular change, configuration and release processes can be applied to the media. There are a large array of tools available. Physical copies go into a secured storage space. Several tools allow version and ownership control of documents. There are also code repositories where codes that were written by the IT service provider can be stored. Access to this code must be managed to avoid any hick-ups during change management and access management processes.
Benefits of a definitive media library
There are several benefits to having a DML. A well-designed DML supports:
- Release & Deployment Management from a centralized storage area
- Availability and Service Continuity by providing the source of all packaged applications and raw media for use in service restoration and disaster recovery procedures
- Automated server provisioning and rationalization
- Asset Management by providing metadata records and license keys relating to software license provision.
- Cataloged request fulfillment, whether it’s a one-off request or a repeated request for updates to the same service.
Having a DML in place may at first seem like a lot of work for little reward, but it really streamlines processes in the Service Transition stage and acts like a security blanket during change management, configuration management, and release management. A DML is a useful ITIL tool that will help an IT service provider to keep records of all their definitive media items in one centralized place where there is complete control over the items in the library. When checking the items into the library, they can be checked for compliance with the company standards. This adds a security checkpoint which ensures that only tried and tested configuration items are used to act on change requests. This helps avoid situations where releases go into the DML and subsequently implementation that are insecure, unlicensed, not supportable by the operations team.
